Biometric authentication in 2026 is strongest when it is treated as a layered way to verify a user, not as a magical proof of identity that replaces every other control. NIST's current digital identity guidance still frames authentication around assurance levels and authenticator strength, while platform vendors and the FIDO ecosystem increasingly use biometrics as local user verification for stronger, phishing-resistant sign-in flows rather than as remotely shared biometric secrets.
That shift matters. The most useful modern deployments keep biometric templates on the device, combine them with hardware isolation and fallback credentials, add liveness detection where spoofing matters, and trigger stronger checks when risk rises. In other words, the real 2026 progress is less about sending fingerprints or faces to giant central systems and more about using biometrics to reduce password friction without sacrificing security or privacy.
This update reflects the category as of March 16, 2026. It focuses on the parts of biometric authentication that feel most real now: face verification, voice biometrics, fingerprint and iris authentication, behavioral biometrics, anti-spoofing, secure local template protection, risk-based authentication, continuous authentication, and passkeys. Inference: biometrics are becoming more useful not because they do everything alone, but because they fit more cleanly into secure, low-friction authentication stacks.
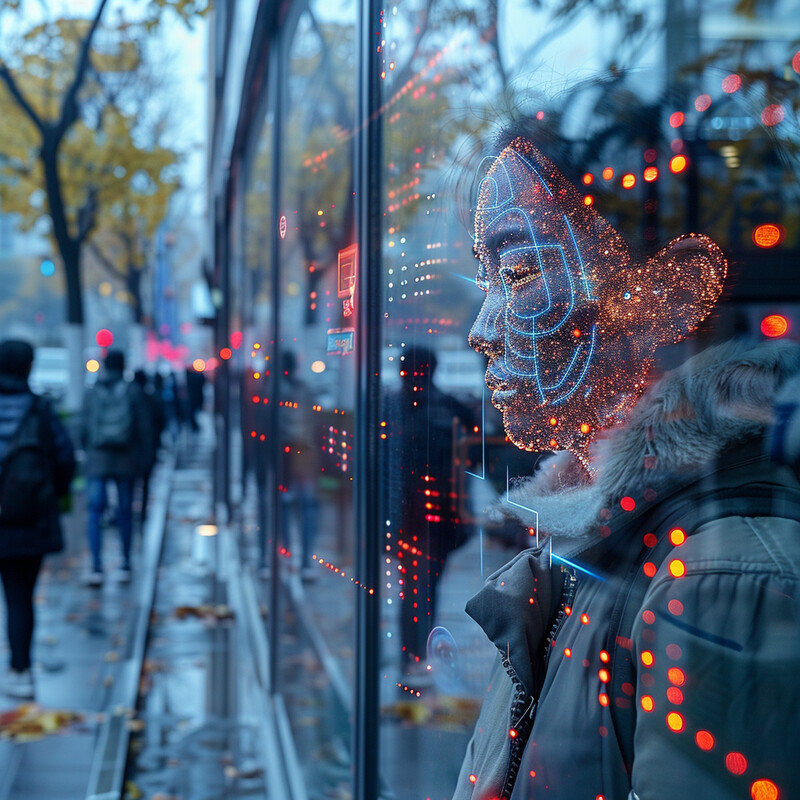
1. Enhanced Facial Recognition Accuracy
Facial authentication is increasingly practical when it is framed as one-to-one verification rather than open-ended identification. That means checking whether the person presenting to the camera matches an enrolled user or document photo, not searching a giant gallery for whoever looks closest. The former is much easier to govern and much more relevant to ordinary authentication.

Microsoft's current Face documentation defines verification as one-to-one matching and separates it from broader identification, while NIST's FRTE 1:1 track continues to benchmark large numbers of face-verification algorithms at strict false-match settings. Inference: the strongest 2026 face-authentication story is not universal recognition. It is that bounded verification has become mature enough to support real account access and onboarding workflows when quality thresholds and review steps are chosen carefully.
2. Adaptive Voice Recognition
Voice biometrics remain useful, but mostly in bounded channels such as contact centers and voice-first service flows. The best systems use ordinary conversation rather than awkward passphrases, yet the rise of voice cloning means voice should usually act as one signal in a broader verification design rather than as the only gatekeeper.

AWS documents Voice ID as a real-time caller-authentication and fraud-risk tool that can enroll a voiceprint from natural speech and, by default, verify a claimed identity from 10 seconds of speech. At the same time, AWS has announced Voice ID end of support on May 20, 2026, while NIST continues speaker-recognition evaluations and best-practice work. Inference: voice biometrics are still real, but the market is signaling that they belong in carefully scoped workflows, not as a universal biometric answer.
3. Fingerprint Analysis Improvement
Fingerprint authentication remains the workhorse biometric because it fits naturally into local device security. The biggest practical improvement is not that fingerprints became newly exotic. It is that modern systems match quickly, store only protected representations, and integrate cleanly with secure hardware and operating-system credential flows.
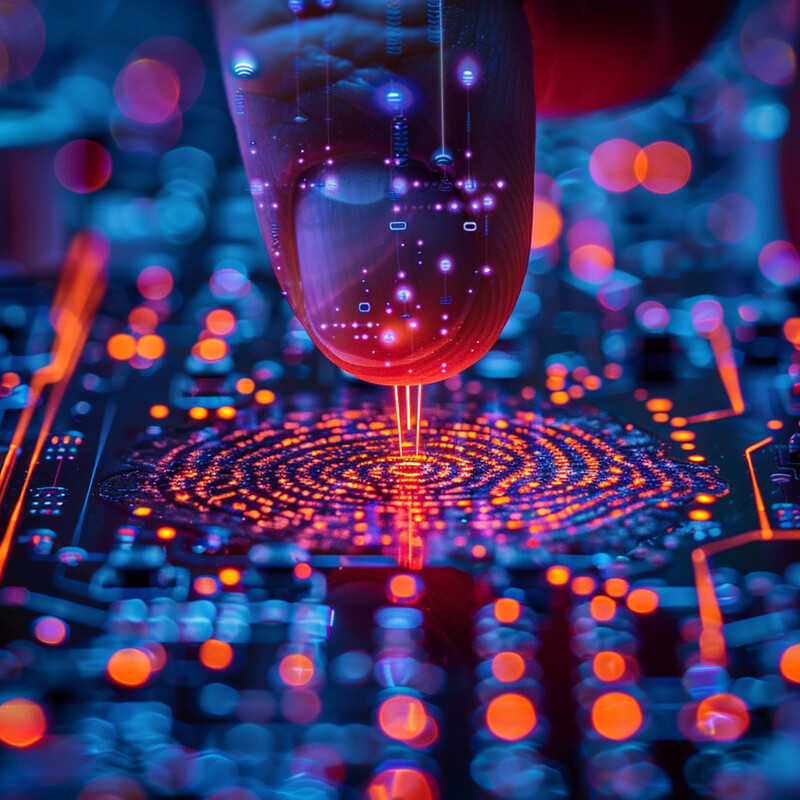
Apple says Touch ID stores only a mathematical representation of the fingerprint, never the image itself, and protects that representation inside the Secure Enclave. Android's biometric APIs likewise distinguish stronger biometric classes and tie strong biometrics to key-generation and high-risk verification flows. Inference: by 2026, the fingerprint story is less about central fingerprint databases and more about high-quality local matching anchored to device security.
4. Iris Recognition Enhancement
Iris and other ocular biometrics remain narrower than fingerprint or face unlock, but they still matter in higher-assurance and hands-free settings. They are useful where gloves, contamination concerns, or stronger matching demands make other modalities less convenient.
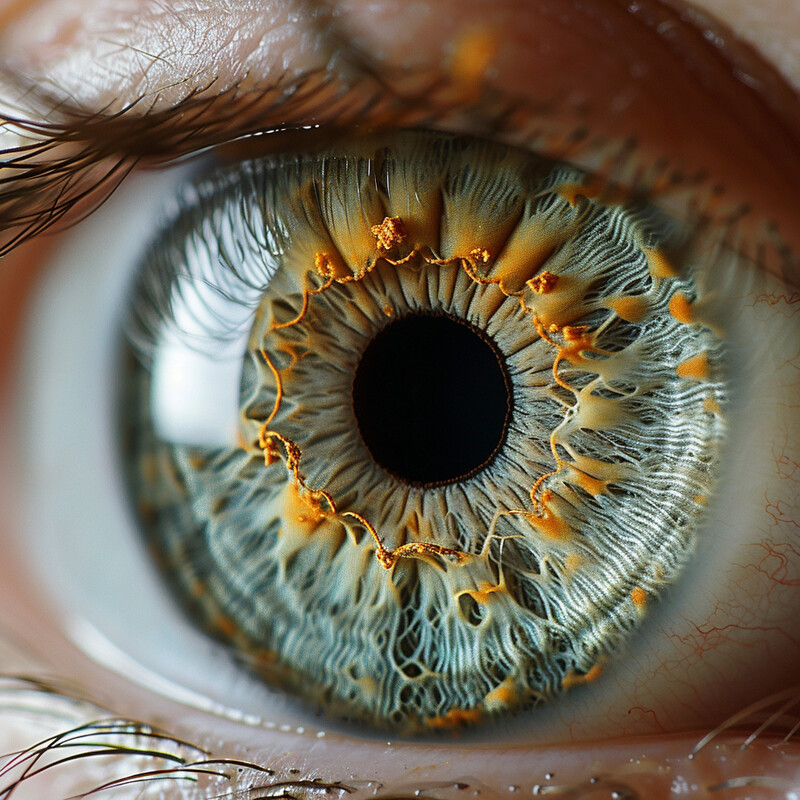
NIST's IREX 10 program remains active as an ongoing evaluation of iris-recognition technology, and Android still treats iris as one possible Class 3 strong biometric modality when it meets the platform requirements. Inference: iris recognition is not the consumer-default biometric in 2026, but it remains important enough to justify formal evaluation and strong-device support.
5. Behavioral Biometrics
Behavioral biometrics add value because they keep watching for consistency after the first unlock. Typing rhythm, swipe behavior, navigation patterns, and device handling do not replace a primary biometric, but they can help a system notice when the person behind an authenticated session no longer looks like the same user.
Microsoft Entra ID Protection says most users have normal behavior that can be tracked, flags suspicious or anomalous activity at user and sign-in level, and uses machine-learning-driven risk levels to decide when stronger remediation is warranted. Inference: behavioral biometrics in 2026 are most useful as a passive risk signal that complements primary authentication rather than pretending to be a standalone proof of identity.
6. Anti-spoofing Measures
Biometric authentication is only as trustworthy as its spoof resistance. Photos, replayed videos, masks, synthetic speech, and other presentation attacks have made plain matching insufficient for higher-risk workflows. That is why modern systems increasingly pair matching with liveness, challenge-response, or other anti-spoofing checks.
AWS says Rekognition Face Liveness is designed to verify that a user is physically present, returns a 0 to 100 confidence score, and should be combined with other factors in a risk-based identity decision. Apple likewise describes Face ID as using depth information and anti-spoofing neural networks. Inference: the baseline for serious biometric authentication in 2026 is not just matching. It is matching plus anti-spoofing plus fallback.
7. Real-Time Decision Making
Users now expect biometric authentication to feel immediate, but that apparent simplicity hides a deeper design change: more of the decision is happening inside protected device pathways. The practical gain is not only speed. It is lower exposure of biometric data and a tighter connection between the biometric check and the credential it unlocks.

Microsoft's Windows Hello Enhanced Sign-in Security isolates the face-matching algorithm with virtualization-based security, encrypts face templates with keys accessible only to that protected environment, and requires secure match-on-sensor hardware for supported fingerprint flows. Inference: what feels like instant biometric login in 2026 is often the result of stronger local isolation, not simply faster matching models.
8. Integration with Other Security Measures
Biometrics are increasingly useful because they are woven into broader risk-based authentication systems. The right question is no longer "Did the biometric match?" but "Given the current risk, is this biometric result enough, or do we need stronger proof?"
NIST SP 800-63B says higher assurance levels require multiple factors and explicitly allows step-up authentication when a higher AAL is needed during a session. Microsoft Entra's sign-in risk policies similarly let organizations require stronger authentication for elevated sign-in risk, and Android's new Identity Check capability can require Class 3 biometric authentication outside trusted places. Inference: the 2026 pattern is adaptive orchestration, not one fixed biometric rule for every situation.
9. Continuous Authentication
Continuous authentication means the system keeps reassessing trust after login instead of assuming one successful check is enough forever. That can involve behavioral patterns, context shifts, risky-session signals, and targeted reauthentication when something changes.

Microsoft Entra says some sign-in risks are detected in real time while others appear offline after authentication, and recommends policies that can require stronger checks every time for risky sessions. Android's Identity Check feature similarly raises authentication demands when the device is outside trusted places. Inference: the useful 2026 model is no longer one login followed by blind trust. It is an authentication session that can be tightened when the surrounding risk picture changes.
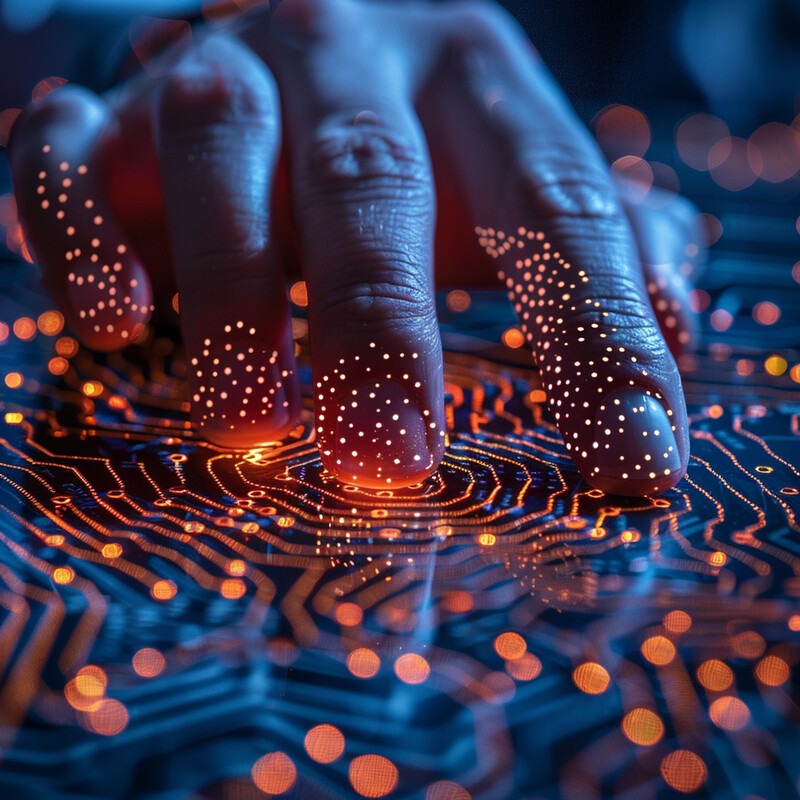
10. Passkeys and Better User Experience
The most important user-experience shift is that biometrics now fit naturally into passkey flows. Instead of asking people to remember and type passwords, modern systems increasingly let them approve sign-in with the same device-unlock gesture they already use. That creates a rare security win that also feels easier.

FIDO says passkeys let users sign in with the same process they use to unlock their device, such as biometrics or a PIN; that passkeys are phishing-resistant by design; and that biometric processing stays on the device and is never sent to a remote server. FIDO also says passkeys leverage multiple factors because the credential is on the device and, when user verification is required, is exercised by a biometric or PIN. Inference: passkeys are the clearest 2026 example of biometrics becoming more useful by being more local, more phishing-resistant, and less server-centric.
Sources and 2026 References
- NIST: SP 800-63B.
- NIST: FRTE 1:1 Verification.
- NIST: Speaker and Language Recognition.
- NIST: IREX 10 Ongoing Evaluation of Iris Recognition.
- FIDO Alliance: Passkeys.
- Apple Support: About Face ID advanced technology.
- Apple Support: About Touch ID advanced security technology.
- Android Developers: BiometricManager.Authenticators.
- Microsoft Learn: Overview: Verification with Face.
- Microsoft Learn: Windows Hello Enhanced Sign-in Security.
- AWS: Detecting face liveness.
- AWS: Use real-time caller authentication with Voice ID in Amazon Connect.
- AWS: Amazon Connect Voice ID end of support.
- Microsoft Learn: Risk detection types and levels.
- Microsoft Learn: Require multifactor authentication for elevated sign-in risk.
Related Yenra Articles
- Identity Verification and Fraud Prevention shows how biometric checks fit into larger anti-fraud and onboarding workflows.
- Facial Recognition Systems goes deeper on the face-verification side of biometric authentication.
- Cybersecurity Measures covers the risk scoring, policy, and response layers that make biometric systems safer in production.
- Contact Center Optimization adds the voice-channel context where speaker verification and fraud monitoring become operationally useful.